Hi everyone,
It’s been a long time but I’m messing around with AWS SAM again. I’m currently converting www.testerwidgets.com into an AWS SAM application. As part of this I needed to add a custom domain. Unfortunately, the doco on how to do this isn’t great so I’m going to share what ended up working for me just in case it helps someone else.
To start, these are the resources that you’ll need in your template.yaml:
Resources:
ApiCertificate:
Type: AWS::CertificateManager::Certificate
Properties:
DomainName: !Sub api-${Stage}.YOUR_DOMAIN.com
ValidationMethod: DNS
ApiGatewayApi:
Type: AWS::Serverless::Api
Properties:
StageName: !Ref Stage
# Allows www.YOUR_DOMAIN.com to call these APIs
# SAM will automatically add AllowMethods with a list of methods for this API
Cors: "'www.YOUR_DOMAIN.com'"
EndpointConfiguration: REGIONAL
Domain:
DomainName: !Sub api-${Stage}.YOUR_DOMAIN.com
CertificateArn: !Ref ApiCertificate
Route53:
HostedZoneName: "YOUR_DOMAIN.com." # NOTE: The period at the end is required
You’ll also need to make sure your reference the gateway from your function:
# This lambda function handles is used to test endpoint availability.
getPing:
Type: AWS::Serverless::Function
Properties:
Handler: src/handlers/get-ping.getPingHandler
Runtime: nodejs14.x
Architectures:
- x86_64
MemorySize: 128
Timeout: 30
Events:
Api:
Type: Api
Properties:
Path: /ping2 # NOTE: AWS overrides the ping command.
Method: GET
RestApiId:
Ref: ApiGatewayApi # NOTE: Make sure you have this referencing correctly.
Description: Responds with 'Pong' if successful.
Now when you run AWS deploy it will continue as usual until it gets to the stage of creating your certificate:

Here it is looking for a specific DNS entry in order to confirm that you own the domain. You’ll need to go into Route53 (or whichever other DNS provider you’re using) and add a CNAME entry with the specified details:
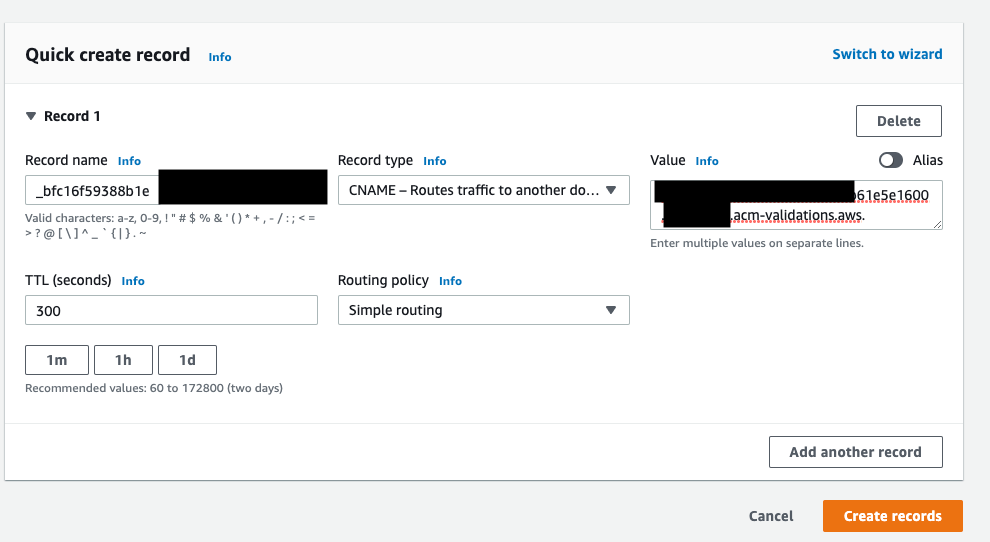
Note that your name and value contents should come from the output of the ApiCertificate job (highlighted in the screenshot above).
Once that’s done you’ll need to wait about sixty seconds for the DNS records to propagate within AWS. You should then be able to access your api using the new domain:

Thanks to the follow github post for the pointers in the right direction: https://github.com/aws/aws-sam-cli/issues/2290
aws sam No hosted zones named found
Note that if you get the error above when trying to deploy please ensure that you’ve added the trailing “.” to your Route53 HostedZoneName in the api-gateway in your template.yaml:
Domain:
DomainName: !Sub api-${Stage}.yourdomain.com
CertificateArn: !Ref ApiCertificate
Route53:
HostedZoneName: "your-domain.com." # NOTE: The period at the end is required